Don’t miss your chance to experience Perplexity’s innovative AI search! Get a year free by 12/31/2025. But be very careful with private questions.
IT
RocketChat support is incredibly awful
You're not prisoners, why do you keep using RocketChat? Here's the answer.
How to remove VirtualVoice books from Audible.com
Audible/Amazon doesn't offer a GUI checkbox to remove AI voiced books from results, but there's an easy workaround which requires no scripts.
Apple Security Theatre Tested
Apple should be protecting our privacy but is not. The security measures they have in place do more to prevent us from securing our computers
For and against frameworks: React, Vue, Angular, Ember, JQuery, Bootstrap, Tailwind, Pure, Ruby-on-Rails…
To require javascript to display "Hello world", a brochure website or even a basic weblog adds complexity for complexity's sake. Go native.
Blackmagicdesign forum real names rule: good policy or privacy violated?
It's hard to run a clean professional public space even without anonymity. People who seek privacy can and should build online personas.
How to Move Fast and (not) Break Things
Start by building automated testing, live monitoring and versioned deployment. Improve your safety systems. Fix the bugs you know. Ship.
How to Type Mac Keyboard Symbols into Forums and Web Pages
Have you ever wondered how to type Mac keyboard symbols like ⌘ and ⌃ from the keyboard. Today you will find out.
The Cost Imperative: Why Western Software Firms Must Embrace AI in Coding
Programming houses who successfully adopt AI to accelerate their productivity will outpace those who don't.
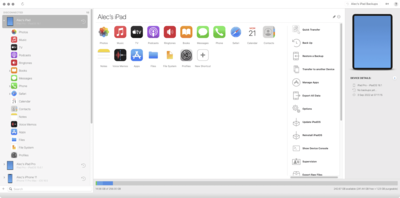
Quick review: iMazing – the missing iPhone management software hidden by Apple
iMazing is the grownups' version of iPhone management, making Apple's enterprise utilities available to end users in an attractive GUI.
Should Websites Publish their Videos in HDR?
The HDR hype is real. But Is HDR a solid AV advance like 4K or a 3D marketing hoax all over again?
How to check the colour bit rate of a video
There's no clear solution but QuickTime Player is a good place to start.
World’s Worst ReadMe or Why Open Source Struggles
This is probably the most user-hostile readme I've ever read.
How to set up MarsEdit 5 for Markdown
MarsEdit 5 is still a bear to set up. When it’s finally working, it’s a fantastic tool for writing and to post to WordPress.2
What AV features do matter when choosing equipment
There's only a few characteristics which matter when choosing AV equipment. By focusing on what matters, you'll enjoy better equipment for less.
AV Industry Audio and Video Scams over the Years
Watch your money carefully. Check any innovation out up close before you jump on board. Spatial Audio is just the latest scam.
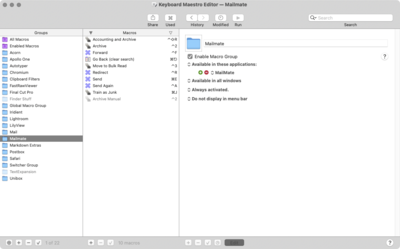
How to change the keyboard shortcuts on macOS
The huge issue with the Apple method is that those shortcuts have to be painfully added by hand on every Mac you own, now or in the future.
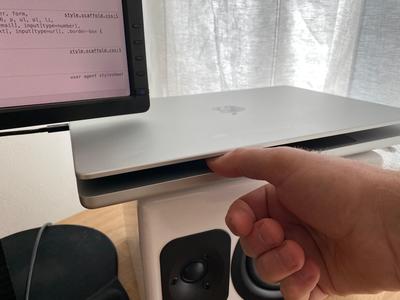
M1 MacBooks and Open Clamshell: Thumbshell Mode
Apple, either let us turn off the screen when in clamshell mode, or open up the API's to let Panaitu build a tool which will do it for us.
How important is the difference between DxO DeepPrime and DeepPrime XD
The difference is not huge. The claims for image improvement are overblown as are the claims about false detail and imaginary textures.
How to troubleshoot a WordPress membership website
The goal of these steps is to solve issues fast and ensure that troubleshooting causes as little pain as possible to the publisher.