Firefox is an open source web browser initially released in 2002 by Mozilla Foundation and its subsidiary Mozilla Corporation. Firefox is well-loved among privacy-minded communities since besides its privacy narrative, it is also highly adjustable, and represents the only major alternative to chromium-based browsers, along with its forks (such as GNU IceCat, Waterfox, Librewolf etc.).
But don’t be mistaken, Firefox just like almost any other browser phones home via telemetry, connecting to the Mozilla servers by default. For instance, just by opening it up after fresh installation, Firefox makes connections to several Mozilla registered domains such as http://www.firefox.com, http://www.mozilla.com, http://www.mozilla.net, http://www.mozilla.org etc.
As concluded in Douglas Leith’s study, Firefox surely calls for several privacy tweaks in order to be considered private:
Firefox sends telemetry which includes identifiers that can potentially be used to link these over time. This telemetry can be disabled, but is silently enabled by default. Firefox also maintains an open websocket for push notifications that is linked to a unique identifier and so potentially can also be used for tracking and which cannot be easily disabled. On mobile devices Firefox sends a long-lived device identifier to backend servers, but not on desktop devices.
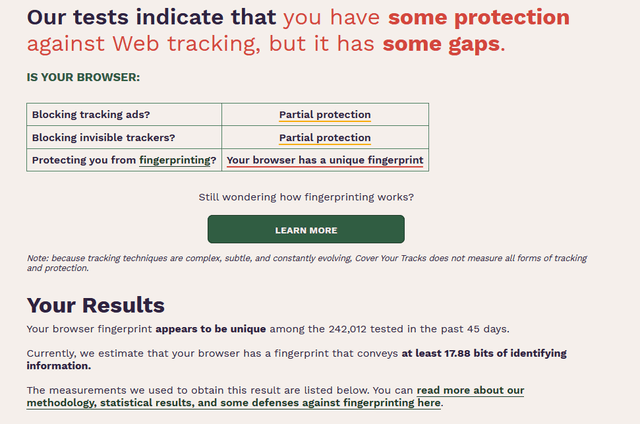
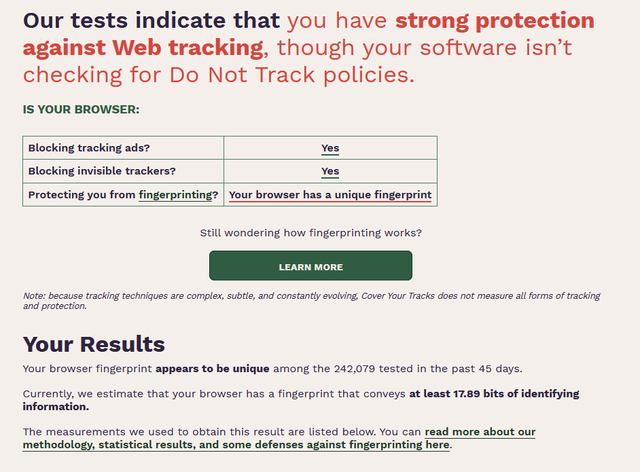
Let’s see EFF’s Cover Your Tracks report for freshly out of the box Firefox in default settings:
While this isn’t a nightmare of Chrome or Edge caliber, results are not satisfactory either. Let’s set Firefox up in a way that will help us stay clear of the stalking.
Basic privacy setup
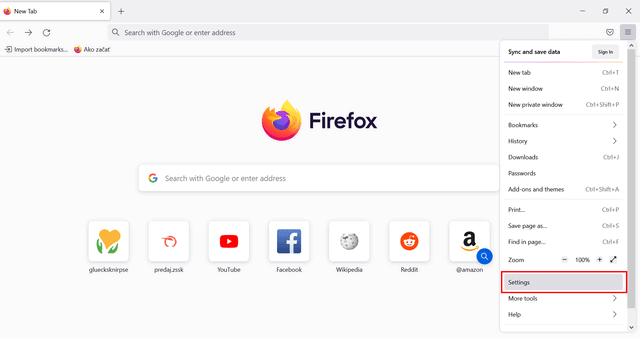
1. open browser settings.
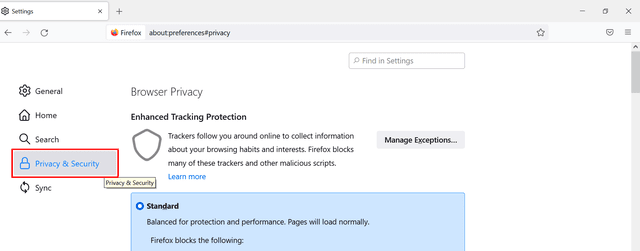
2. Choose the Privacy & Security section.
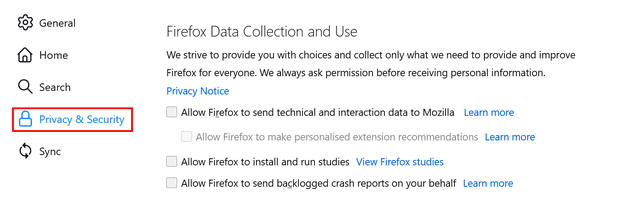
2. Then scroll down to Firefox Data Collection and Use to make sure that each of the telemetry settings is disabled.
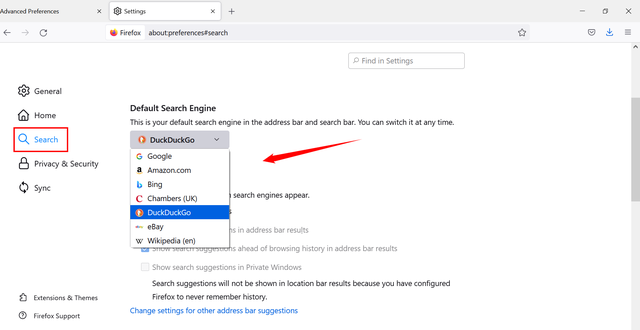
3. Another important step in privacy configuration is to set up your default search engine.
Firefox defaults to Google for financial reasons; Google pays them rather generous amount of money – around $400-$450 million annually, to keep their spying search engine as default.
Go to Search section in browser settings and choose your default search engine. It’s definitely not easy to choose the most private search engine, since data harvesting has become a big deal over last couple of years. To address this shortly, from the offered ones, only DuckDuckGo allows you to hope for some kind of privacy. For more detailed insight into the topic, check out our article about the most private search engine.
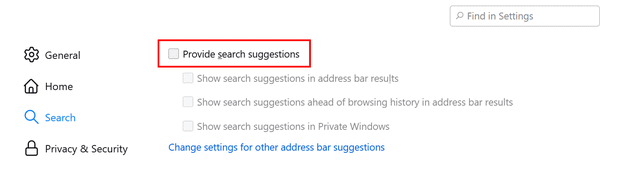
4. Furthermore, opting out of sending your data over to search engines by search suggestions should come naturally as a next step in privacy-building.
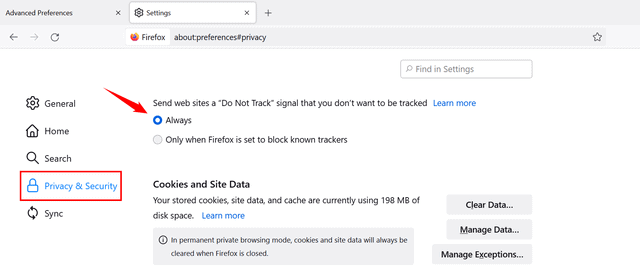
5. Sure, websites are clearly starved to track you. Adjusting their user interface to improve their goal completions, targeting personalized ads or even selling your data to third parties nicely contributes to their revenue, but in Firefox you can mostly avoid these tricky practices by tweaking your browser. There is a a nice option to enable Do Not Track:
Sadly, this “industry standard” hasn’t worked well since Windows 10 (i.e. 2015). Why? Do not track is optional, with no legal force. There’s a very short list of companies which respect the “Do not track” token. Here’s most of the list as of 2019: Twitter, Medium, Reddit, and Pinterest.
6. Happily, there are stronger, user-enforceable options available to prevent website tracking. Start by enabling Allow Enhanced Tracking Protection in Privacy & Security settings. Firefox recommends standard protection, as it blocks cross-site tracking cookies, social media trackers, cryptominers, and fingerprinting.
You can opt to change to Strict protection, but remember that this may break some sites, but will do much more to protect your privacy. My own experience is that most sites in 2021 do just fine with strict protection enabled in Brave. The exceptions are very bad websites like NFL.com, overloaded with too much technology, too many services, and endless advertising.
Of course, you can also opt for custom tracking protection.
advanced settings optimization
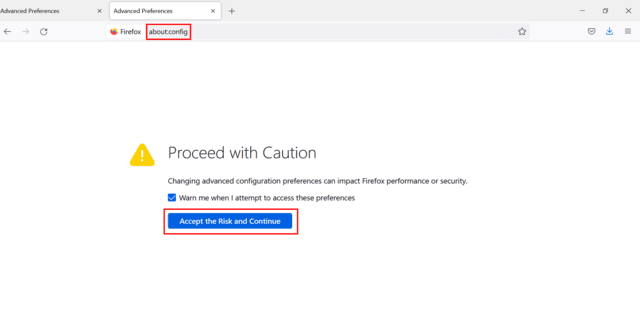
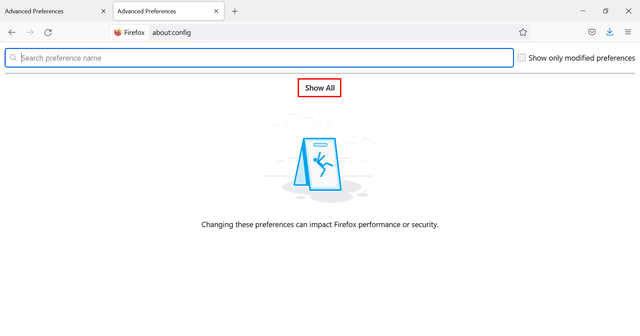
After this basic set up, you can configure Firefox in more advanced way by typing about:config in the address bar.
1. Ignore the scare tactics warning.
2. Since Firefox apparently doesn’t trust its end users, you’ll have to click show all button despite you accepted the risks in the previous step.
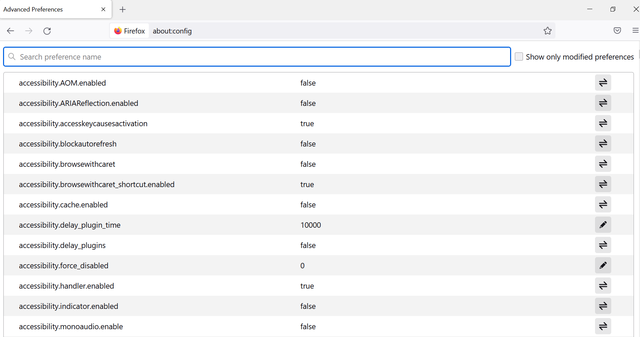
3. Having done that, what seems like an endless list of various options shows up. Here you can improve your privacy a bit further.
There’s a set of values to be turned false by double clicking on them.
4. First step includes turning off geolocation by setting the value false once you type geo.enabled into the search bar.
5. Many privacy ethusiasts are adamant that another step should lead to disabling Google Safe Browsing. While this bold move imposes a security risks (this function protects you from phishing and malware websites), it radically improves your privacy, because your data won’t be sent to Google anymore. Once again, the choice is up to the user. If you have deep reason to value your privacy, you’ll turn off Safe Browsing.
If you wnat to disable safe browsing, set these values:
browser.safebrowsing.enabled = false
browser.safebrowsing.downloads.enabled = false
browser.safebrowsing.malware.enabled = false
On the other hand, these settings can be really hazardous, because this way you’re getting stripped of the protection against malicious phishing and malware websites. Paradoxically, GSB is one of more private Safe Browsing clients compared to MS Smartscreen or even Opera Fraud and Malware Protection. To learn more check our comprehensive article which also explains Safe Browsing topic in further detail along with primary source references. In result, I wouldn’t recommend opting out Safe Browsing. Furthermore, Firefox uses separate “cookie jar” for cookies set by Safe Browsing servers, so they won’t mix up with regular browsing session cookies.
Personally, I browse with Safe Browsing enabled, as the risk of not having access to the industry-standard blacklist worries me. Really that blacklist should be in someone else’s hands other than Google and it shouldn’t be necessary to send private data to Google in order to benefit from blacklists of known malware websites.
6. Following tweak disables visited websites from getting notifications if you copy, paste or cut something from the webpage:
dom.event.clipboardevents.enabled = false
7. In the next round, we can take care of the cookies. Type network.cookie.cookieBehavior and network.cookie.lifetimePolicy in the search bar.
In case of the cookies behaviour, opt for the value 1, which only accepts cookies from originating sites but blocks third party cookies. Please remember that if you block all cookies, it will render many websites broken to the point of uselessness.
The lifetime policy is up to you, but the safest solution is assigning value 2, which deletes cookies once the session is over (once you close Firefox).
Here you can see further descriptions:
network.cookie.cookieBehavior:
0 = Accept all cookies by default
1 = Only accept from the originating site
2 = Block all cookies by default
3 = Block cookies from unvisited sites
4 = New Cookie Jar policy
network.cookie.lifetimePolicy:
0 = Accept cookies normally
1 = Prompt for each cookie
2 = Accept for current session only
3 = Accept for N days
8. You can also improve your set up, by disabling offline cache. Do this by typing browser.cache.offline.enable in the search bar and set value to false.
9. After setting so many values to false, the time has come to set some to true. When it comes to disabling Web GL, it’s smart to choose true value, since this feature represents potential security risk.
webgl.disabled = true
It’s highly unlikely that 98% of web browser users would require 3D animations to browse the web, read articles or watch videos, so there’s very little loss here by not having WebGL available.
10. Other settings to take care of include:
- privacy.resistFingerprinting (true) which enables Firefox’s native fingerprint protection.
- privacy.trackingprotection.fingerprinting.enabled (true), which provides additional fingerprint protection.
- privacy.trackingprotection.cryptomining.enabled (true) protects you from cryptominers.
- privacy.trackingprotection.enabled (true) blocks known third party trackers.
- privacy.firstparty.isolate (true) strengthens your privacy by isolating cookies to the first party domain, and prevents tracking across multiple domains.
11. Tracking information about your microphone and camera are yet another pieces of puzzle in fingerprinting. You can stop sites from gathering these information by setting false value next to media.navigator.enabled.
12. Another important thing to do is to stop sending anything you’re typing to the search engine. To do so, it requires you to change the value next to the browser.search.suggest.enabled to false.
Those search suggestions do not come free: the price is having everything you type or paste in your URL bar sent to your search provider. The data is sent, even if you change your mind about the query.
13. Next, DRM (digital rights management) is also an issue. It basically controls what can users do with digital media. DRM restricts unauthorized usage or spreading of copyrighted digital content. As explained on DefectiveByDesign.org:
When a program is designed to prevent you from copying or sharing a song, reading an ebook on another device, or playing a single-player game without an Internet connection, you are being restricted by DRM.
The shady part of this function is that it monitors and controls our activity and interactions with digital media. Inevitable part of it is collecting IP addresses, but not only that. It is tracking additional user information via download, browsing activities or subscription service etc. Understandably, we should be concerned about this enough to opt this out in the browser settings like this:
media.eme.enabled false
It disables the playback of DRM-controlled HTML5 content and there are some sites where content playback isn’t possible without enabled DRM. So while this setting contributes to your privacy, it once again undermines usability.
My suggestion here would be to have one browser which is DRM-enabled to allow using Netflix, Prime Video, Audible and other DRM protected services and in your other browsers to disable DRM plugins.
14. Next, WebRTC is a feature that provides browsers and apps with real-time communication via API, so it allows audio and video communication to work inside web pages. Cool function, indeed, but it also costs you some privacy, since it leaks your real IP address even when you are using VPN or TOR. Once again, based on your preference, usability vs privacy, you can either opt it out or not:
media.peerconnection.enabled
WebRTC is less of an issue if you are chatting with people whom you already know. It’s not a big deal if your mother, your friends or even your work colleagues know your home IP. Not true, just by having WebRTC enabled, any website you visit can obtain your true physical IP regardless of VPN. Was WebRTC the secret sauce in the Netflix crackdown on VPN post-2015? Recommendation: WebRTC should be toggled on when needed or again, enabled only in the known-sources browser.
15. Preventing Firefox from prefetching DNS requests also comes as a wise step. Advanced domain name resolution may simprove page loading speed, it also imposes several privacy risks. To opt out of it, set *network.dns.disablePrefetch value to true. To prevent pages from being prefetched by Firefox set network.prefetch-next value to false
16. Other than that, you can disable telemetry by setting these values false, so Firefox will not collect usage statistics and performance reports:
toolkit.telemetry.unified toolkit.telemetry.enabled datareporting.healthreport.service.enabled datareporting.healthreport.uploadEnabled
After applying suggested privacy tweaks in my then default Firefox Browser I repeated EFF’s Cover Your Tracks test and this is the result:
Results still could be better. It’s arguable that Mozilla is losing its plot. By accepting funding by Google and trying to make users to extend the default telemetry by newly released Rally extension, Firefox is continuously losing my trust.
On the other hand, it still stays the only suitable alternative against Chromium-based browsers, thus representing a tiny piece of something unique among Google’s hegemony, while still offering wide variety of personalisation and privacy customsation to the viable level.
See our guide for Opera.
See our guide for Brave.
Leave a Reply